HP Wolf Security reported that in Q1 2022, nearly half of the malware stopped was packaged in Microsoft Office file formats. However, they also documented a recent attack where the malware was packaged in a PDF file to attempt to evade detection.
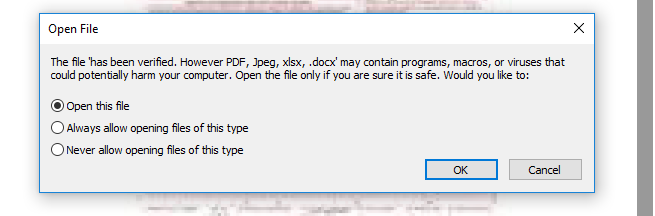
Once the PDF was opened, Adobe Reader prompted the user to open a DOCX file. The DOCX file was named “has been verified. However PDF, Jpeg, xlsx, .docx”, so when the warning from Adobe Reader that the file might contain malicious programs, macros, or viruses, pops up, it makes the user think they are opening a “verified” or “safe” file.
Choosing “Open this file” allows the malicious DOCX file that was embedded in the PDF to connect to a remotely-hosted server to download and execute another document containing OLE objects. One of these OLE objects contained shellcode that exploited a remote code execution vulnerability in Equation Editor (CVE-2017-11882). This shellcode, which was encrypted and obfuscated to avoid detection, downloaded additional malware to infect the device with the Snake Keylogger.
The full writeup of the attack is available on the HP Threat Research Blog: https://threatresearch.ext.hp.com/pdf-malware-is-not-yet-dead/
Explanation of CVE-2017-11882 from the SOCPRIME Blog: https://socprime.com/blog/cve-2017-11882-two-decades-old-vulnerability-in-microsoft-office-still-actively-leveraged-for-malware-delivery/


